Bill would turn government’s vulnerabilities equities process into law
This report first appeared on CyberScoop.
There’s a bill in the works that would codify the U.S. government’s vulnerabilities equities process into law, CyberScoop has learned.
The legislation intends to add clarity, transparency and a level of consistency to the VEP, a secretive framework which guides when and if a federal agency will notify a technology firm of an unknown, exploitable software flaw discovered by the U.S. government.
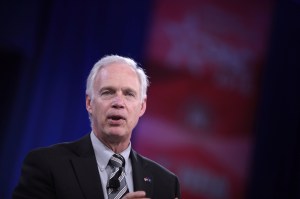
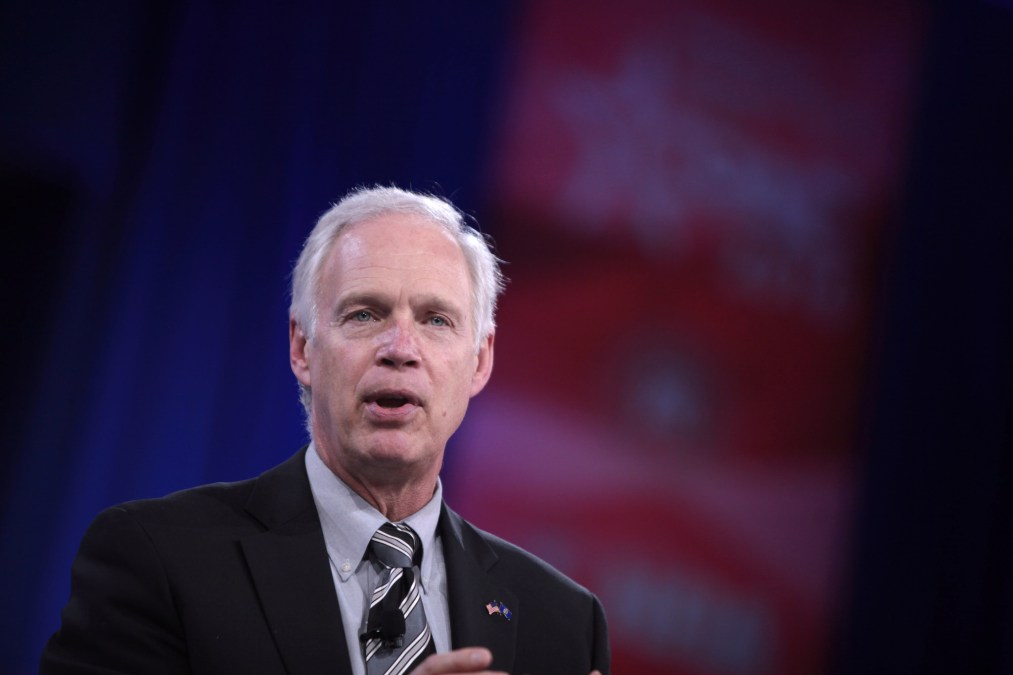
The bill is being sponsored by Sens. Brian Schatz, D-Hawaii, and Ron Johnson, R-Wis. Spokespeople for both senators confirmed the existence of the bill, but would not provide additional details.
The VEP has come under fire in recent years due to, at least in part, the exposure of classified material concerning government hacking operations. Exacerbating this situation is the fact that the private sector remains largely in the dark with regard to the VEP’s disclosure criteria and the identity of individuals who sit on its multi-agency review board.
An early draft of the legislation offers a standard definition for what exactly constitutes a “software vulnerability” according to the federal government. The bill also includes language that clearly designates who is on the VEP’s review board. Neither the White House nor National Security Council would have a seat on the board under the early draft of the bill.
Under the legislation, a central office or authority would be responsible for reaching out to companies affected by the framework — though it remains unclear who exactly should hold that position. Additionally, the bill — which is now receiving comments from policy experts and private sector partners — mandates that future VEP decisions require some input from the Privacy and Civil Liberties Oversight Board, an independent agency established under the 2007 law that implemented recommendations of the 9/11 Commission.
The Privacy and Civil Liberties Oversight Board, or PCLOB, was designed to be comprised by five members, each tasked with blowing the whistle when U.S. spy agencies disregard privacy and other civil liberties. The Intercept reported in March that the commission was “basically dead,” with just one active member still involved.
Very little is publicly known about how the VEP works, despite being established in the first term of the Obama administration.
Former White House Cybersecurity Coordinator Michael Daniel first publicly acknowledged the VEP process in 2014, after news reports suggested that the government kept a critical vulnerability secret that was related to the popular OpenSSL cryptographic software library. The VEP, Daniel wrote at the time, would be “reinvigorated” under Obama.
In the past, the default for the VEP has been to err on the side of disclosure, even by the super-secretive National Security Agency, according to a comprehensive research report conducted by Columbia University last year. That mindframe isn’t likely to change during the current Trump administration, Neil Jenkins, director of the Homeland Security Department’s Enterprise Performance Management Office, or EPMO, said in February during a panel discussion at the 2017 RSA cybersecurity conference.
“It is not within our national interest to build up a stockpile of vulnerabilities to hide behind and to use for intelligence or law enforcement purposes. We have to get those out to make sure that systems are secure,” Jenkins said. “But the process does recognize that there are some vulnerabilities that we need to keep, that we need to use for national security purposes.”
“The process is still in use, it is in regular use, and we are having meetings about these things on a pretty regular basis. And I would say, as of right now, we are still in the mode of responsible disclosure under the current administration,” said Jenkins.