Inside the lucrative operation that runs Cerber ransomware


Once a ransom is paid, Cerber’s authors take great measures to ensure their payments do not reveal who is responsible for the attacks.
A team of Israeli security researchers has uncovered the inner workings of a leading form of ransomware, detailing a wide-ranging affiliate payment program and a bitcoin-mixing operation that shields actors from ever being discovered.
Experts from Check Point Software Technologies and IntSights published research Tuesday that shows how the syndicate responsible for Cerber ransomware has grown into an illegal, organized enterprise, infecting more than 150,000 victims and netting $195,000 in profit in July alone.
Cerber differs from other ransomware in that its proliferation is a matter of design. The malicious software is being sold on the dark web as part of an affiliate program, which allows fairly unsophisticated actors to purchase a kit to launch a ransomware campaign against a target. In return, the authors take a 40 percent cut of any paid ransom. Other popular ransomware versions, such as Locky, have been kept in use solely by the malware’s authors.
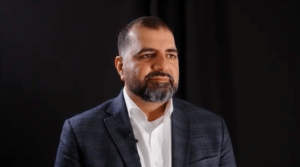
Attack kits are sold on a web portal that allows attackers to launch campaigns and keep track of attack attempts, how many were successful, how many victims paid the ransom, and if they are eligible to receive bonuses for recruiting more affiliates.

An analytics dashboard that tracks profit related to the Cerber ransomware. (Check Point)
“The interesting thing here is each one of these affiliates have their own attack vector and targets,” said Maya Horowitz, group manager for Check Point’s threat intelligence division.
Last month, researchers witnessed hundreds of campaigns across the globe, including one that targeted victims in South Korea. That campaign, which Horowitz believes to have been part of an operation tied to malvertising, made up nearly 40 percent of all worldwide Cerber attacks.
Attackers can choose whether to disseminate Cerber through exploit kits — like Magnitude, Rig or Neutrino — or attach a malicious payload through an email phishing attempt. Horowitz said the research team witnessed one such phishing campaign that sent emails to companies in Germany alleging to be job applicants sending resumés.
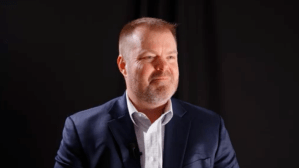
Once a ransom is paid, Cerber’s authors take great measures to ensure their payments do not reveal who is responsible for the attacks. Victims make their payment to a unique bitcoin wallet, which is controlled by the ransomware’s authors. That payment is then pushed through a bitcoin mixing service — a third party that breaks the connection between a bitcoin address sending coins and the address they are sent to — to anonymize the cryptocurrency. It is then moved to other wallets, while pushing a portion to affiliates based on their program’s payout.

A breakdown of how bitcoin moves through the Cerber affiliate program. (Check Point)
The researchers believe Cerber is of Russian origin, due to a configuration file that prevents it from attacking targets in Armenia, Azerbaijan, Belarus, Georgia, Kyrgyzstan, Kazakhstan, Moldova, Russia, Turkmenistan, Tajikistan, Ukraine and Uzbekistan. This follows a similar trend spotted by FireEye researchers in July who found attackers monitored a number of countries in Eastern Europe and Central Asia to keep the ransomware outside of certain legal jurisdictions.
Despite ransomware primarily affecting U.S. hospital systems and local police departments, Horowitz said those who buy Cerber kits are not looking for any particular target. Mostly, attackers are just using the “spray and pray” mentality, hoping their efforts end in a ransom payoff.
[Read more: Feds confident in fight against ransomware]
“These actors are in it for the money,” Horowitz said. “They send the ransomware to the largest possible number of targets and hope for the best. With the exploit kit, all they need to do is purchase another service that is a redirector of an exploit kit and just have it send to the infection chain.”
Through their research, the experts were able to find a hole in Cerber’s code to build a decryption tool that will allow victims to forgo paying a ransom.
Horowitz also said she hopes the research gives pause to attackers who, as more researchers publicize their actions, are more likely to shut down in fear of being identified.
“The more threat actors feel like someone is really on their back or has a lot of information on their operations, they sometimes step back,” she told FedScoop. “They are afraid someone will connect the dots and figure out who they are. The more details published, the more chances that the threat actor will decide to quit.
Contact the reporter on this story via email at greg.otto@fedscoop.com, or follow him on Twitter at @gregotto. His OTR and PGP info can be found here. Subscribe to the Daily Scoop for stories like this in your inbox every morning by signing up here: fdscp.com/sign-me-on.