Many federal agencies still weak on information security, GAO report finds

In a time of rampant cybersecurity concerns, a recently released Government Accountability Office report expresses frustration with the information security at federal agencies.
The congressional watchdog is quick to remind readers that it’s hardly a new thing: “GAO first designated federal information security as a governmentwide high-risk area 20 years ago.”
The vast majority of the 24 agencies covered by the CFO Act are weak in five key control areas — access controls, configuration management controls, segregation of duties, contingency planning and agency-wide security management, the report states.
“GAO and IGs have made hundreds of recommendations to address these security control deficiencies, but many have not yet been fully implemented,” the report says.
The report’s two stated objectives are assessing the information security practices at the 24 CFO Act agencies and examining “the extent to which agencies with governmentwide responsibilities have implemented their requirements under the Federal Information Security Management Act of 2002 as amended by the Federal Information Security Modernization Act of 2014,” or FISMA.
The security assessment yielded some eye-catching statistics. For example, a full 24 of 24 agencies had weak access controls — “the policies and practices that limit or detect access to computer resources” — and agency-wide security management — “the policies, processes, and practices that provide a framework for ensuring that risks are understood and that effective controls are selected, implemented, and operating as intended.”
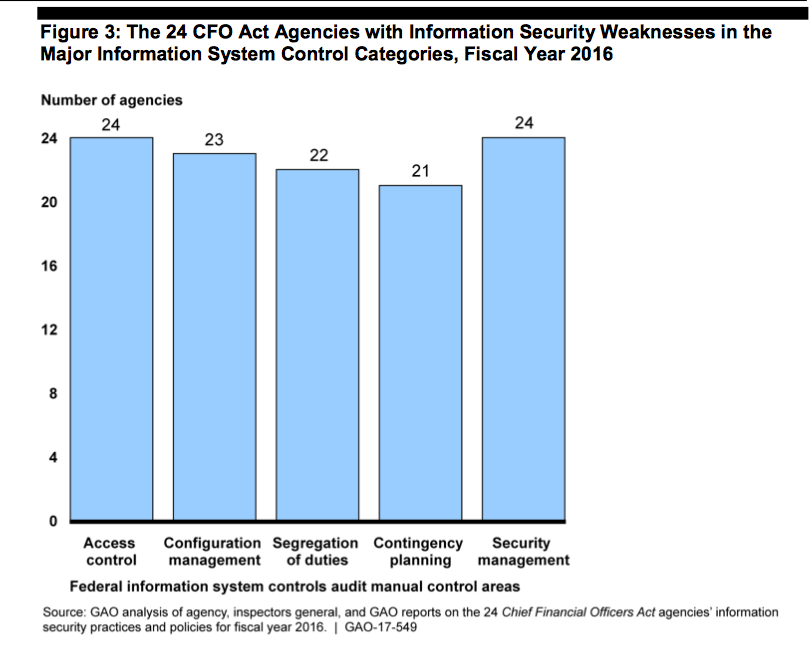
(Screenshot)
On the second aim, of evaluating agencies with governmentwide responsibilities to oversee the implementation of FISMA — like the Office of Management and Budget — the outlook is a little brighter.
Pursuant to FISMA, the OMB uses a maturity model developed by the Council of the Inspectors General on Integrity and Efficiency to assess information security practices. However, what OMB does not have is a way to ascertain whether this assessment is helpful.
“Until an evaluative component is incorporated into the implementation of the maturity model, OMB will not have reasonable assurance that agency information security programs have been consistently evaluated,” the report states.
GAO concludes by suggesting that OMB create and implement such an evaluation.
“We are not making new recommendations to address these weaknesses because we and the inspectors general have previously made hundreds of recommendations,” the report states, once again reminding readers this is a longterm issue. “Until agencies correct longstanding control deficiencies and address our and agency inspectors general’s recommendations, federal IT systems will remain at increased and unnecessary risk of attack or compromise.”
OMB “generally concurred” with the recommendation.