Securing the future of federal networks with open standards
For the past few years, consolidation has been a key buzzword within federal government circles, but the concept isn’t really all that new.
Back in the early 1940s, General Dwight Eisenhower, while tasked to build an Army, mandated the consolidation of weaponry, equipping soldiers with M1 Garand semi-automatic rifles. It was a controversial and disruptive move that upended the traditional way things were done; the relationship between an infantryman and his weapon was not one to be trifled with lightly. It was necessary action that ultimately provided a sound foundational building block for World War II combat and beyond.
Today’s version of consolidation looks like the Defense Information Systems Agency’s Joint Information Environment initiative, which is converging various networks while bringing together disparate technologies. Those technologies have to work together if DISA is to achieve its ultimate goal of a consolidated and more efficient and cost-effective network.
Now, war is not just on physical terrain but in cyberspace as well. Threats are becoming more prevalent and sophisticated, and bad actors are highly motivated.
The possibility of a compromised Joint Information Environment is very real, because while General Eisenhower’s soldiers were able to adapt to using a common rifle, it can be extremely challenging for network administrators to converge and combine closed, proprietary software solutions that are inherently incompatible. This incompatibility can create significant security holes while undermining DISA’s goals for a more streamlined network.
Unfortunately, many Department of Defense agencies are still heavily reliant upon proprietary legacy software that was installed years ago. The perception is that it’s too costly and complex to upgrade to open, software-defined systems.
In reality, it’s too costly not to upgrade to these solutions, particularly considering today’s threat landscape, and administrators cannot afford to ignore the signals that it’s time to consider deploying open network solutions.
The first and most obvious signal is a malfunctioning piece of equipment. Any malfunction could expose the agency to risk, and it’s important for network administrators to understand why their solution has stopped working.
It’s nice to think that every time a company releases a software update that the latest version will be immediately installed, but that’s simply not reality. Even if it were, proprietary software is generally updated too infrequently for our rapidly changing cybersecurity peace of mind. But the truth is that agencies cannot afford to be more than one software revision behind, and even that is the lowest possible watermark. Just being good enough is not nearly good enough at all.
Any consolidation project is susceptible to software compatibility issues, but giant initiatives like the Joint Information Environment run an even greater risk due to the sheer complexity of all of the different components that are converging. If many of those components are running on proprietary, closed systems, there’s going to be a greater likelihood that they simply will not work together effectively.
Software built on open standards addresses both of these issues. Harnessing the collective power of the open source development community, coupled with the expertise of companies who specialize in open software to provide timely support and guarantee the quality, allows users to have the latest updates and patches that can immediately and easily be installed.
Open software has the additional benefit of transparency, allowing users to understand exactly what is going on with the software they use and deploy. This gives the user complete visibility of the vulnerability and how it is fixed, something that is hard to achieve with conventional black-box solutions.
And by its nature, software built on open standards is designed to be compatible with many different tools and options. This, coupled with the transparency of open source software, will help the DOD form a usable, functional and highly flexible network that allows users to securely share and access information across agencies.
Fortunately, the move toward the cloud has necessitated acceptance of open standards within the government. Today, many federal network administrators understand that in order to provide cloud-based services and applications they must be operating on open platforms. That commitment to openness must continue if our government networks are to remain efficient, secure and future-ready.
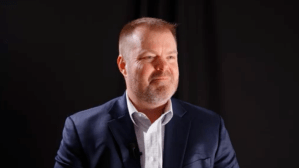
Tim Solms is the Vice President, US Federal and Managing Director of Worldwide Government at Juniper Networks. In his role he manages the sales, engineering, and operations for the Federal Government’s Defense, Intelligence, and Civilian businesses as well as the Federal Systems Integrators and partners. Additionally provides executive oversight and support for Juniper’s Government businesses worldwide.