Meet the man responsible for teaching some of the NSA’s best young hackers

The National Security Agency is an enormous organization by nearly any corporate standard, with more than 35,000 employees. Former Deputy Director Chris Inglis once joked that the spy agency is “the biggest employer of introverts.” More frequently though, the NSA refers to itself as the largest employer of mathematicians. In recent years, while the U.S. has continuously confronted new threats in cyberspace, the agency has increasingly become a training ground for young, talented, highly educated computer security professionals.
Underlining the NSA’s race to hire the best and brightest is a list of 213 universities that the spy agency has designated as “National Centers of Academic Excellence.”
These schools offer a myriad of computer security training programs, each providing a stepping stone into the secretive agency. In this context, Carnegie Mellon University is to the NSA what the University of Alabama is to the NFL. And Professor David Brumley is CMU’s Nick Saban.
“As NSA’s Security Education Academic Liaison (SEAL) to Carnegie Mellon University since 2010 and knowing several CMU alumni that work at NSA, the quality of the individual that graduates from CMU is very high. They have made solid contributions to our mission,” said Ryan Agee, an NSA technical director.
Speaking with CyberScoop for this story, Brumley said hackers and their practice had gotten a bad rap. Between our questions, he passionately and often without pause defended the broadly defined tradecraft known to many as “offensive cybersecurity.” The public, Brumley said, shouldn’t look at “hacking” in the context of “bad or good” but rather as this necessary skill set, independent of a moral label.
“He’s sort of a legend around campus,” joked Tiemoko Ballo, a computer security graduate student at the Pittsburgh-based university who is considering a career with the NSA. “Whenever he’s teaching a class, students rush to register because they realize how valuable that experience is.”
The professor is among a small, select group of academics to hold a government clearance. He often travels between D.C, Northern Virginia and Pennsylvania to speak at security events and interact with defense officials.
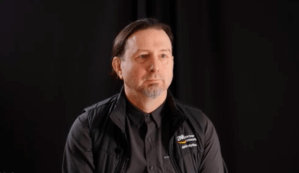
An energetic scholar largely unknown to news headlines but adamantly revered by academics, spies and technology executives alike, 41-year-old Brumley is credited with designing a unique curriculum that teaches students how to hack into devices in order to hone their defensive security skills.
Getting a clearance, navigating the federal application process and ultimately securing employment at the Pentagon take time, effort and persistence, Brumley empathized. It’s understandable if a student with debt prefers the private sector’s rapid recruitment process, he said.
Brumley said he does not encourage CMU students to join the Defense Department over the private sector. Even so, he said he would reach out personally to the department to advocate on a student’s behalf if necessary.
“I’d call them, someone I know, and tell them: ‘What are you doing?’ Don’t mess this up, call them back,’” Brumley said during one phone interview.
In the past, a significant portion of the NSA’s Tailored Access Operations unit — an elite group of government hackers — has held a diploma from Carnegie Mellon. As of 2013, between 10 percent and 15 percent of TAO personnel were CMU alums, former NSA officials told CyberScoop.
Former U.S. intelligence officials aren’t shy in their praise for Brumley, crediting him with shaping some of the nation’s very best hacking talent.
“The program he’s running at CMU is producing experienced graduates that typically would not have this kind of technical mastery without several years on the job,” said former NSA technical director Bryan Smith. “Brumley has broken down the art of memory corruption and exploit writing into a reproducible science.”
“If I were recruiting at the agency, or for technical development roles, I would be doing everything I could to land every one of his graduates,” said Smith.

David Brumley teaching a class
Under the NSA’s current reorganization initiative known as NSA21, TAO exists in a different capacity — without the name — having been fused together with the Information Assurance Directorate, the spy agency’s defensive group. While the names have changed, the skills required to exploit targets and protect the country remain similar.
“He is most certainly making a positive impact in the space in two key ways: automating vulnerability discovery and exploitation and building top technical talent,” said Smith, now CTO of CyberGRX, a private sector firm specializing in cybersecurity automation and advanced analytics.
Cut From a Different Cloth
A new global arms race focused on cybersecurity is already underway between the U.S. and its rivals, said Michael McFaul, a former U.S. ambassador to Russia and former special assistant to President Obama on the National Security Council. In this development sprint to design both innovative technology and guiding policy, McFaul, a now professor at Stanford University, told CyberScoop that America boasts a distinct advantage because it is home to many of the world’s best educational institutions.
Graduates coming from top computer science programs across the U.S. are commonly recruited by the likes of Microsoft, Google and Facebook, among other tech giants. A select few join the intelligence community and are tasked with hacking into foreign computer networks.
Brumley’s students are coveted by the federal and private sectors alike. Competition to secure their services is fierce.
To attend CMU as a full-time student — regardless of degree or specialization — first requires a nearly perfect secondary-school transcript and SAT score. Undergraduate computer science students at CMU will earn, on average, $108,000 in their first year out of school.
Since 2001, the U.S. government has awarded Carnegie Mellon with more than $22 million in funding as part of the Scholarship for Service program, a highly selective scholarship program for U.S. students. Organized by the Office of Personnel Management, SFS is designed to “increase and strengthen the cadre of federal information assurance professionals that protect the government’s critical information infrastructure.”
Students that commit to government service through the SFS program are often able to avoid debt from the university’s annual undergraduate tuition bill of $70,000.
While school is in session, CMU SFS students must attend presentations every Wednesday hosted by recruiters from different federal agencies, including the FBI, CIA, NSA and numerous technology research institutes.
Only about 146 students graduate from the undergraduate computer science program per year, with the vast majority moving on to the private sector for corporate internet brands like Google, Facebook and Oracle, Brumley said.
Yet graduates have also gone onto work in the U.S.-CERT, NSA, CIA, FBI, the State Department, Johns Hopkins Advanced Physics Lab, Lawrence Livermore National Laboratory and the SLAC National Accelerator Laboratory.
“For me, right now, I think it’s between the NSA and an FFRDC [federally funded research and development center] like MITRE,” said Ballo, a first year SFS student with prior experience in the private sector.
“The NSA is attractive to me because of their unique mission,” Ballo explained, “what do they call it? The government has a ‘monopoly on violence’ … If you want to do offense that’s really the only option.”
Tourney Titans
Beyond the boundaries of Fort Meade and CMU’s campus, Brumley’s pupils are shaping another industry: the competitive circuit of computer hacking tournaments.
Brumley coaches Carnegie Mellon’s hacking team, the Plaid Parliament of Pwning — a highly skilled group of students who break into electronic systems for sport. Founded in 2009, PPP is a dominant force.
Over the last several years, PPP has won the National Cyber Analyst Challenge and multiple DEF CON “Capture the Flag” and “Crack Me If You Can” contests.
Some of the world’s most talented young cybersecurity professionals — notably, both U.S. citizens and foreign nationals — have chased championships with the PPP crew under Brumley’s guidance. Computer security luminary George Hotz — perhaps best known for breaking into the original Apple iPhone at just 17 years old — competed with PPP at the 2013 and 2014 DEF CON hacker conference.
At the most recent DEF CON, the group competed in DARPA’s inaugural Cyber Grand Challenge under its “Mayhem” moniker. The CGC contest represented a groundbreaking experiment in that all the participants created autonomous supercomputers built to simultaneously patch vulnerabilities in their own architecture while also hunting for flaws in rivals’ computers. What unfolded during the contest was nothing short of a major advancement in the development of artificial intelligence-enabled cybersecurity. Mayhem’s system topped its competitors, taking home a $2 million prize.
Brumley attributed the consistent success of both PPP and more broadly, CMU’s computer science department, to its staff and students. The professor — much like his admirers in the intelligence community — explained that recruiting top talent is key to refreshing the ranks and consistently winning tournaments.
“We train elite high-end technical experts who can find new vulnerabilities so that they are fixed before attackers can use them,” Brumley told CyberScoop. “I don’t think any university excels at this like we do.”
In 2012, Brumley founded PicoCTF, a 18,000-person hacking competition for middle and high school students. The tournament has given CMU’s computer science program early access to promising coders. Past PicoCTF events have been sponsored by Trend Micro, Boeing, Qualcomm, the National Science Foundation and the NSA.
For the past three years, PicoCTF’s top 10 teams have each received personal letters of recommendation from Brumley to attend Carnegie Mellon. Most are accepted and go on to attend the university, he said.
One Defense Department official recently described PicoCTF as a sort of “NFL combine” for CMU. Brumley said he appreciated the comparison.