New CIO Aaron Weis wants to redeem Navy after damning cyber review
New Navy CIO Aaron Weis‘s job was created as a response to a departmentwide cybersecurity review that painted a damning picture of the service’s IT and cyber readiness. Now, weeks into the role, Weis hopes that at some point he gets the chance to redeem the Navy by showing improvement in a follow-up review.
“I’m hopeful that at some point we’ll get an opportunity to get a better grade, and I’m sure we’ll do that,” Weis said Wednesday at an AFCEA DC luncheon. The report, he said, “did not paint a flattering picture of the current state of cybersecurity at the Navy.”
As the March 2019 review noted, “Competitors and potential adversaries have exploited DON information systems, penetrated its defenses, and stolen massive amounts of national security” intellectual property. It pointed at a poor cybersecurity governance structure as one of the major flaws, which led Secretary Richard Spencer to call for the creation of an empowered CIO role at the department level of the Navy.
Since just days into taking on that role in late September, Weis has been occupied with questions from Congress about how he’s working to remediate the Navy’s flawed cybersecurity. “They’re aware of it. They’re going to continue to ask,” he said, detailing meetings he has planned this week and next with staffers and members of the Senate Armed Services Committee to discuss the service’s efforts.
“I think we can only improve. The good news is we can only go up from here,” Weis said.
And it largely starts with emphasizing a culture of cybersecurity across the entirety of the Navy, not just in IT shops, he said. Cybersecurity “is more than sensoring equipment and applying yet another layer of software. I think it importantly is about changing the culture. We have to move from a culture of security by compliance to a culture where security is embedded in everything that we do and it’s how we operate. … It has to become part of everyone’s job.”
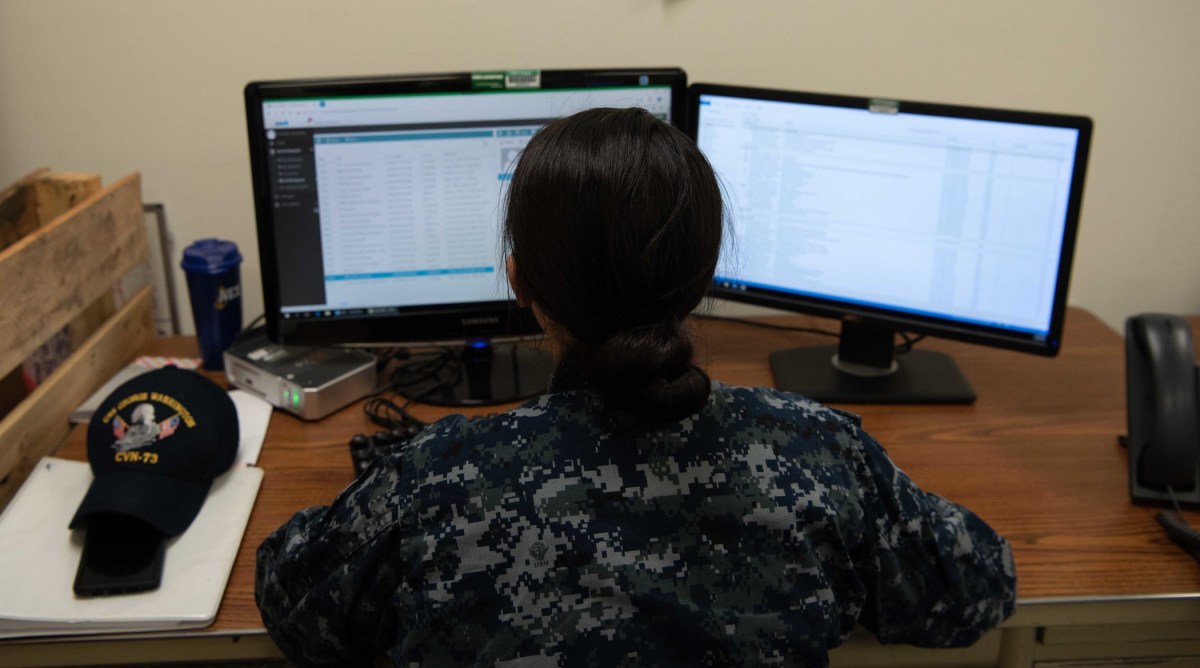
Securing the lower tiers of the supply chain
The Navy review also pointed to an insecure IT supply chain as a major vulnerability.
“The DON’s dependency upon the [defense industrial base] presents another large and lucrative source of exploitation for those looking to diminish US military advantage,” it says. “Key DIB companies, primes, and their suppliers, have been breached and their IP stolen and exploited. These critical supply chains have been compromised in ways and to an extent yet to be fully understood.”
Weis’ vision for securing the supply chain involves what he calls IT “defense.”
“We have to be able to lean into our defense industrial base and partner with them to really secure our information that lives in the supply chain of the Department of the Navy. If you look at it, we are losing our information. And not to the tier ones, they are very mature, the Lockheeds and Raytheons of the world have really talented security people who work with them. But when you get down to tier two and three of that supply chain, we’re not where we need to be.”
Of course, this problem is not unique to the Navy. The Pentagon has been developing the Cybersecurity Maturity Model Certification to create accreditation standards contractors must meet if they want to do work with any part of the DOD.
Weis said with the CMMC, DOD has “the right perspective on this.”
“I’m a big believer in that model,” he said, referencing that it’s “table stakes” for other industries, like those for chemical or automobiles. “And they’re not going to pay for you to go get certified. You’re going to do that on your own, because you want to do that work. And that’s kind of a ticket to entry.”