NOAA evaluating multi-factor authentication for apps and devices
Editor’s note: This story has been updated to include additional information about the Open-Architecture Data Repository and NOAA’s supercomputing improvements.
The National Oceanic and Atmospheric Administration is exploring multi-factor authentication beyond its network as it looks to strengthen cybersecurity in accordance with the federal zero trust strategy, according to its chief information officer.
Zach Goldstein told FedScoop his agency already requires Common Access Cards (CACs) and personal identification numbers to authenticate to its network but continues to perform comparative analyses of multi-factor authentication (MFA) solutions for applications and devices.
“We’re looking at things other than CAC cards, things that are intelligent tokens — that know who I am, that can exchange certificates with a certificate server, that can be easily revoked, that can have multiple kinds of privileges,” Goldstein said.
Goldstein added that cybersecurity is his “first priority,” in keeping with the White House’s Cybersecurity Executive Order issued in May 2021, and that he hopes to select a token for app and device authentication by the second quarter of fiscal 2023.
NOAA is also increasing supply chain risk assessments of Software as a Service — looking not only at the firm but what they buy and use for services — under Goldstein, who’s been with the agency 17-and-a-half years and CIO since 2015.
Goldstein wants to expand NOAA’s use of the cloud in a way that further improves the agency’s cyber posture while shedding light on how migration is progressing.
“We have an initiative to create a Cloud Program Management Office (PMO), one of whose jobs will be to provide me and NOAA leadership with that answer,” he said.
Assuming the funding for the office within the president’s fiscal 2023 budget stands, Goldstein hopes to launch it by the end of that fiscal year.
According to Goldstein, NOAA was the second federal agency to move its email and calendar to a public cloud, Google Apps for Government, in 2011, and since then the agency has migrated websites, help desk ticketing and global device management.
“It became very clear that we needed to have more discipline going to the cloud and more efficiencies because people were duplicating each other by having to learn how to do a security evaluation of going to the cloud, learn how to authenticate to the cloud, figure out how to communicate and get my data to the cloud,” Goldstein said. “And they were also using different contract vehicles.”
The CIO agreed to authorize NOAA offices’ migrations with the expectation that once his team implemented centralized cloud services streamlining and lowering the cost of the process, they’d use those instead.
“It became very clear that we needed to have more discipline going to the cloud and more efficiencies.”
– NOAA Chief Information Officer Zach Goldstein
NOAA now offers a standard way of getting to the cloud; authenticating using its identity, credential and access management (ICAM) service; and contracting with the three large service providers — Google, Amazon and Microsoft — and others. The Office of the CIO’s Cyber Division evaluates cloud offerings once for universal use across NOAA, accelerating offices’ migrations, but the Cloud PMO will make it so they don’t have to consult separate experts for each step in the process.
A Cloud PMO will also help offices take advantage of NOAA Open Data Dissemination (NODD), which allows for “extremely inexpensive” egress to the public, Goldstein said.
The White House proposed a large funding increase for the Office of Space Commerce in its fiscal 2023 budget, which if accepted by Congress would elevate it to a staff office receiving IT support from the OCIO.
Goldstein expects to indirectly advise on, provide perimeter security for and oversee the cloud-native Open-Architecture Data Repository, which processes tracking data on space objects to predict and assess risk of collision. This information will improve space situational awareness for commercial and civil space operators. A requirements analysis is ongoing, so the operational cost hasn’t been calculated yet.
“Because the cloud is available and they know how to do it, we know how to do it — we’re going to help the Office of Space Commerce with this — they’ll be able to get that capability in the hands of the world faster,” Goldstein said.
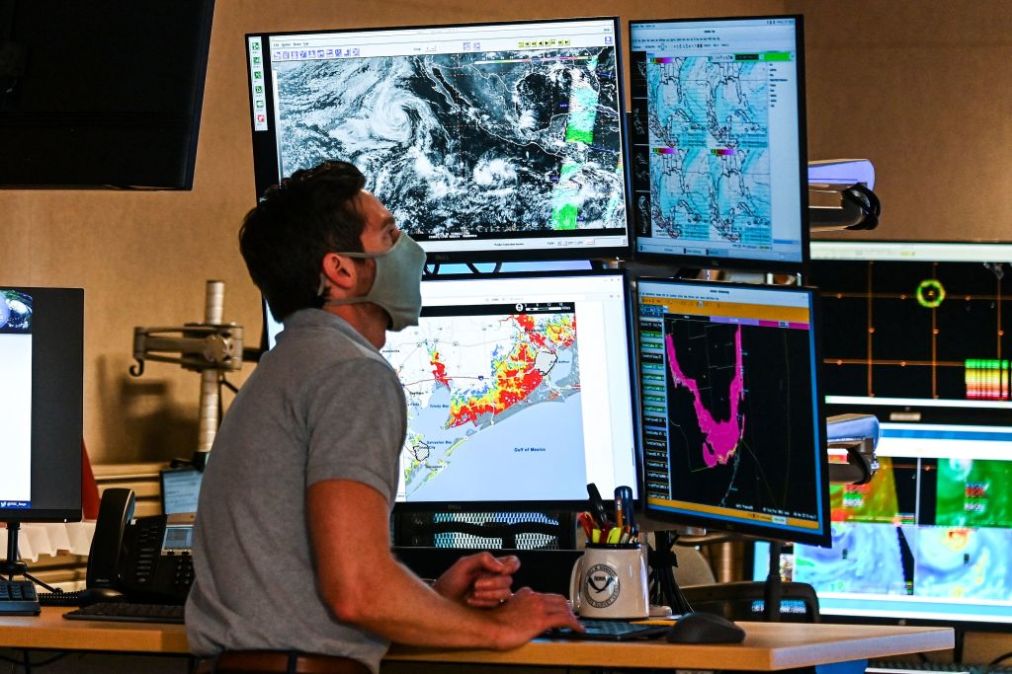
The cloud is also freeing up NOAA’s IT professionals — previously stuck patching, scanning and performing domain controller work — to improve weather forecasting model accuracy and speed.
Supercomputing improvements that continue to be made by NOAA have increased capacity for forecasting three times over and should lead to 30% growth in research computing by the end of 2022, but research and development could benefit from even more, Goldstein said. The agency’s objective is to get enough capacity to perform all NOAA research, and enable focusing these applications down to what should be operationalized.
“We’re not there yet,” Goldstein said. “But we’re getting closer.”






