Office of the National Cyber Director needs federal funds to meet hiring goals

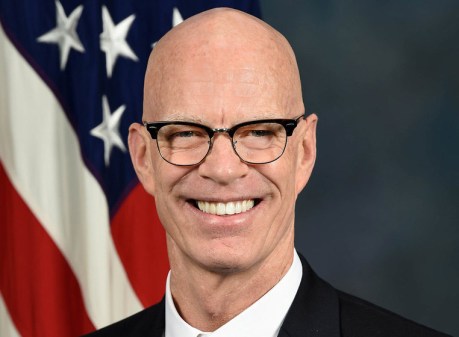
The Office of the National Cyber Director built a “robust” talent pipeline but cannot use it to hire critical personnel until it receives congressional appropriations, according to Director Chris Inglis.
Speaking before the House Homeland Security Committee on Wednesday, Inglis said he expects to onboard 25 staff members by December and a “full complement” in fiscal 2022 — provided Congress passes a spending bill.
The $1.75 trillion reconciliation bill faces resistance from Sen. Joe Manchin, D-W.Va., over its size and Medicare and climate provisions, and the holdup continues to constrain ONCD staffing.
“Beyond the constraint this places on our ability to hire key staff members, make necessary procurements and acquisitions, and find permanent office space for our future, the lack of appropriations inhibits our ability to plan and delays our ability to quickly and fully make the expected contributions of the national cyber director,” Inglis said.
That includes ONCD’s plan to expand on its first strategic intent statement, released Oct. 28, with a comprehensive list of priorities and objectives for years to come, he added.
The Cybersecurity and Infrastructure Security Agency is similarly working to fill “a lot” of vacancies, in part, by assessing its hiring process for fixable inefficiencies, said Director Jen Easterly.
New Cyber Talent Management System authorities come into force Nov. 15 that will help CISA close its talent gap, Easterly said.
“That will give us greater flexibility to hire based on aptitude and attitude, not based on degrees or certifications,” she added. “And it will allow us to be able to pay closer to market.”
CISA recently announced $2 million in grants split evenly between the NPower and Cyber Warrior organizations to extend talent pipelines into diverse communities, with plans to target historically black colleges and universities in the future, Easterly said.
Congressional appropriations will be critical to those efforts as well and CISA and ONCD’s joint effort to streamline the government’s response to cyber incidents. CISA is tasked with partnering with sector risk management agencies to respond to sector-specific attacks, yet the Department of Energy was designated the lead agency after the Colonial Pipeline ransomware attack — despite the Transportation Security Administration’s jurisdiction over pipelines.
Inglis was quick to point out neither he nor Easterly were in their roles when that decision was made.
“From this day forward, from the moment we got here, we strongly believe that the playbook should be followed,” Inglis said. “That when we allocate roles and responsibilities … policy matters.”
ONCD will eventually spearhead longer-term efforts to develop qualitative and quantitative measurements of cyber activity conducted against the government, he added.
In the meantime the national cyber director told lawmakers there’s been a “discernible” decrease in cyberattacks from Russian-backed hackers, since the summit between President Biden and Russian President Vladimir Putin in June.
“It’s too soon to tell whether that is because of the material efforts undertaken by the Russians or the Russian leadership,” Inglis said. “It may well be that the transgressors in this space have simply lain low, understanding that this is for the moment a very hot time for them, and we need to make sure that continues to be the case.”