Quantum computing is coming for your encryption, it’s a matter of when
Everyone knows the age of quantum computing is coming, but no one knows exactly when.
When it does, even the most secure encryption on the planet likely will be shattered. The security and policy implications of that coming revolution were the topic for a panel of academic, commercial and government stakeholders gathered Tuesday at The Hudson Institute as part of Washington, D.C., CyberWeek.
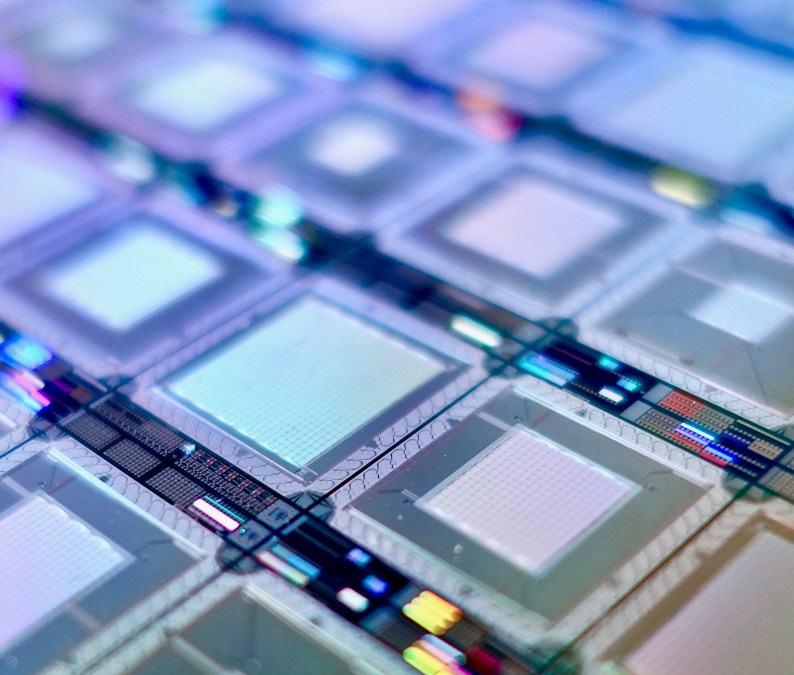
Because experts speculate modern computing is quickly pushing against the physical limits of traditional hardware, countries are beginning to spend more on research in developing quantum computing and communications.
“We’re getting down to the quantum limits [of microchips],” said Warren Miller, professor of physics at Florida Atlantic University. “This signals the need that you can’t do business as usual anymore. And if you can control the understanding of information and communication and secure it, this is where future national security relies on that.”
Because quantum computing is based on encoding data into the superposition of states and creating quantum bits, or qubits, rather than the ones and zeros in the binary digits of electronic computers, quantum computers would be able to crack the large-number Rivest–Shamir–Adleman cryptography currently in wide use.
“So you can think of cryptography as a machine that takes in the belief of the difficulty of this problem and turns it into security, turns it into trust,” said Aaron VanDevender, chief scientist and principal at the Founder’s Fund.
“But is something comes along that were to dispel that belief, then the whole edifice of public key cryptography would crumble. The math would still work, all of our computers would still be performing those calculations, but all of the tangible benefits that we derive from it would suddenly evaporate.”
‘It’s all over the world’
While the U.S. remains one of the global leaders in quantum computing research, other nations are making the push. The symposium’s speakers repeatedly pointed to China’s Sept. 11 announcement that it was building a $10 billion quantum applications research facility as a sign of the importance of developing a strategic edge in the field.
“The race is on,” said Scott Totzke, CEO of the ISARA Corporation. “And the investment is going on globally. It’s not something where we just see this is the United States and Russia and China. It’s all over the world and we are seeing billions of dollars being invested.”
The commercial sector has also gotten engaged, with cloud service providers like Google, IBM, and Microsoft making large investments in quantum hardware.
“Quantum computing will manifest in the cloud,” said Michael Brett, CEO of QxBranch. “We’re already a mixed-hardware environment in the cloud. What we are seeing is each cloud service provider is providing specialist hardware for particular problems.”
But while innovation is on the move in several pockets of the commercial and public sectors, the national security imperative of developing quantum computing is compounded by the advancements of other nations.
“I think America needs to be prepared for the, how can I say this, countries starting with ‘C’ and with ‘R’,” said Sean Kwak, SK Telecom’s Quantum Technology Lab leader. “We have to be prepared for their quantum computer threat.”
A National Initiative
To move the football on quantum computing advancement, Arthur Herman thinks the U.S. needs to tie the innovation of the commercial and academic arenas with the research and support of the government in a reimagining the Manhattan Project model of World War II.
“This has to be a way in which this becomes movement that takes place not in just certain discrete areas that are going to be affected by quantum technology, but really starts to shape a generation who are prepared to take quantum technologies to the next level and push it forward where it needs to be,” said Herman, a senior fellow at the Hudson Institute.
That includes collaborating with traditional intelligence allies like the United Kingdom, Australia, Canada and New Zealand as well as others.
Ultimately, Herman said, this collaboration must move forward to protect the security and trust of our society.
“These systems rest on a belief and trust that the systems installed now will work and are resistant to attack and are resistant to collapse,” he said. “What we’ve seen is that the classic cryptography systems, the ones based on public key cryptography, are doomed. That process then is what comes next?”






