Pentagon taking action to boost cybersecurity down the supply chain
The Department of Defense is making a push to enhance its cybersecurity by certifying and strengthening the cyber-hygiene and capabilities of small businesses that are several steps removed from the Pentagon in the contracting process.
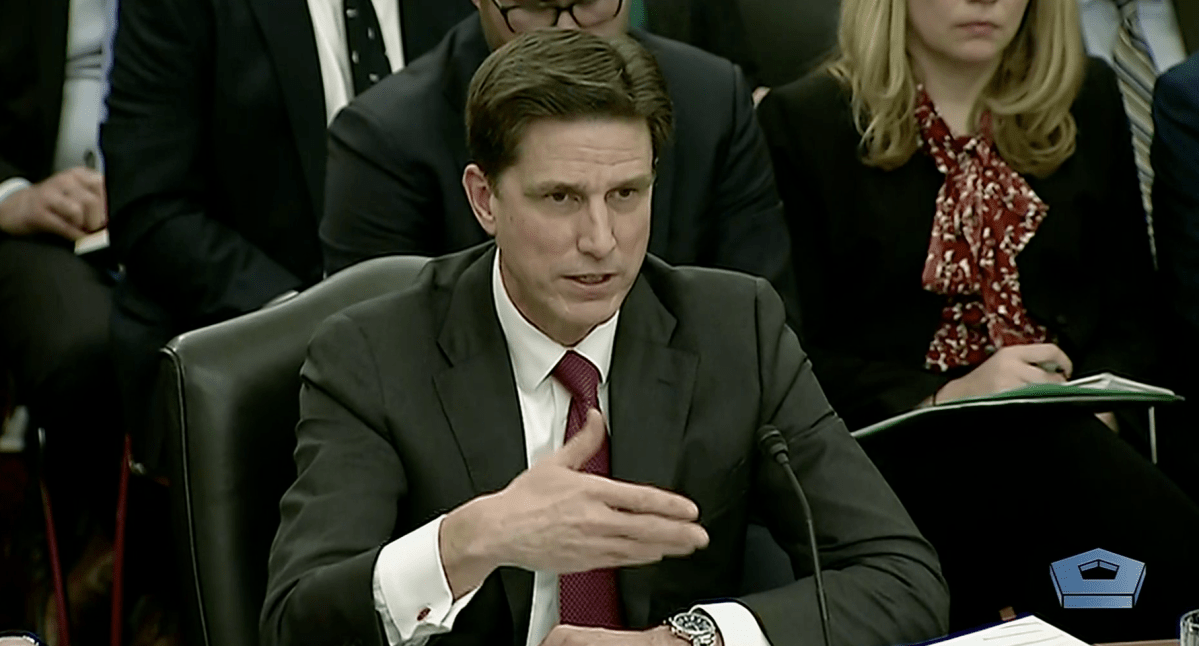
CIO Dana Deasy told the Senate Armed Services Committee this week about new efforts the Pentagon is exploring to strengthen — and build confidence in — the cyberdefenses of subcontractors further down the supply chain. A new program is getting results, Deasy and other witnesses said, but the DOD is also having focused conversations about how and where it can find help.
Ellen Lord, undersecretary of Defense for acquisition and sustainment, leads a program that reports directly to the deputy secretary on ways to create a system to certify the cyberdefenses of subcontractors, in compliance with National Institute of Standards and Technology standards.
In 2017, the Pentagon began holding its direct contractors to higher standards under the NIST compliance. But generally, those contractors bring in other suppliers to do work with them, and often those subcontractors call in other subcontractors under them, making it difficult for DOD to ensure those smaller teams are operating securely.
“This problem is not necessarily a tier-one supply level,” Deasy said. “It’s down when you get to the tier-three and the tier-four” subcontractors.
He added: “Where the issue breaks down is that as you go down to those various subcontractors, do they understand, [are they] equipped, have the knowledge and the capabilities to defend themselves, and what is it we should be doing more to help them learn how to defend themselves at those tiers?”
Lord’s task force is “stepping through the entire way we handle our contractual relationships, our notification of problems, our forensics when we do have a problem, to improve upon that,” Deasy said.
It starts with subcontractors conducting a cybersecurity self-certification. The task force is trying to then figure out a way to build confidence against that certification — creating a “closed-loop system where we can go out and validate what it is they sell us assessed against.”
Validating every single certification, however, is an impossibly heavy lift. So, Deasy said, “there’s discussions right now on what is the right approach on doing that, given that trying to get to every single member of that supply base might be overly challenged. So how do you sample, and how do you do this in a way where you start to get confidence?”
One solution to that challenge might be bringing in a third-party to do that validation. “What has happened in private industry, which is what we are now looking at for the DOD, is actually a process of identifying, possibly even certifying, companies that can play the role, that can follow the NIST standard and actually go in and look at a second-, third-tier supplier,” the DOD CIO said.
The task force is “in the early discussion of how we might do that,” and Deasy said he “has been advising them on how this has been done elsewhere.”
DOD also wants to do more to help subcontractors — ones that are more vulnerable but don’t have the resources address that — build up their cyberdefenses and improve hygiene.
“If you look at what it takes today to do good cyber-hygiene to stay ahead of the adversary, we know many of the second- and third- or fourth-tier supply base simply doesn’t have the wherewithal to do that,” Deasy said. “We have some thoughts underway on how we can bring them into, whether it’s a cloud or an extension of our network, we can fortify them with services that we provide. We are in the very early days of that. But you should know we’re in active conversations of how to do that.”
There’s also the case that technology can bear some of this subcontractor burden. Deasy sees an opportunity for artificial intelligence and machine learning to vet subcontractors.
“There is definitely going to be value in looking at how do you take the entire supply base, the NIST standards, the hygiene problems we see, and can you apply AI to this problem to start to identify where you may most likely are going to experience problems inside your supply chain,” he said. Though there’s no active program to support that yet, Deasy said, “I would suggest this is a good case where we can apply machine learning to looking at this problem.”
During the same hearing, Deasy and his colleagues at the DOD made clear Tuesday that they’re getting impatient with the military’s IT security posture and that 2019 will be a year of action on the Pentagon cyber front.






