Agencies moving forward on TIC 3.0 without finalized policy
The Office of Management and Budget is eyeing more Trusted Internet Connections 3.0 pilots, but less clear is whether they’ll happen before the federal policy is finalized.
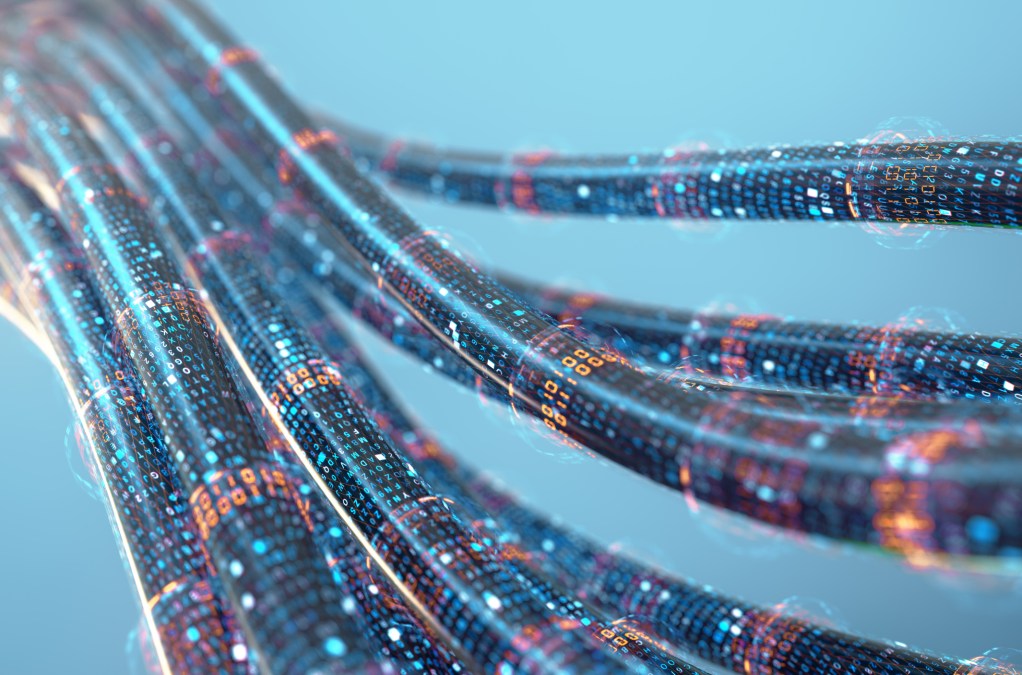
In December, OMB released a draft of TIC 3.0 introducing new use cases like Platform-as-a-Service and software-defined networking (SDN) in a wide area network to improve security as network perimeters become increasingly hard to define in the cloud.
Several TIC 3.0 pilots are ongoing, but the only one that’s been publicized is a Small Business Administration effort to marry the cloud with SDN and cybersecurity. SBA is looking into the native cybersecurity cloud providers give them and indicators that will be helpful to other agencies, Jim Russo, telecommunications manager at the Office of Telecommunications Services, said Monday at a General Services Administration event.
“The [TIC 3.0] draft gives us a pretty good idea of where it’s going, and we’re encouraging agencies to go ahead and create their requirements, start working with [the Cybersecurity Infrastructure Security Agency], bring things to us, and put their requirements out there for industry to take a look at and come up with solutions that may work out,” Russo said. “We’re going to keep moving forward, even though the policy is not final, and when it is we’ll sort of catch it on the fly.”
CISA is heading up the Government TIC 3.0 Working Group establishing guidelines with the next step for agencies being zero-trust networking. TIC 3.0 sets agencies up for zero trust, which involves assigning trust scores to users and datasets and granting access to said data when those scores align, Russo said.
Networking solutions won’t be “cookie cutter” for most agencies, he added, largely due to differing legacy systems that need replacement sooner than later.
In the cloud, traffic comes from multiple vectors necessitating a hybrid network and security, said Allen Hill, director of telecommunications services at the Office of Telecommunications Services within GSA.
“As the agencies begin modernizing … it’s going to change how we apply security on top of that,” Hill said. “And it’s important to think about this now because if you don’t put the necessary security in place … it’s going to leave us open to malicious attacks.”
Hill expects network migration will take three to five years with TIC 3.0 providing agencies with increased flexibility.
Exactly when TIC 3.0 will be finalized remains up in the air.
“As far as prognostication on when that policy may go final, I don’t want to be flippant, but your guess is as good as mine,” Russo said.