‘Poor information technology implementation’ blamed for CPSC data exposure
Convoluted software applications at the Consumer Product Safety Commission are ultimately to blame for the agency’s unauthorized disclosure of the personally identifiable information of roughly 30,000 consumers.
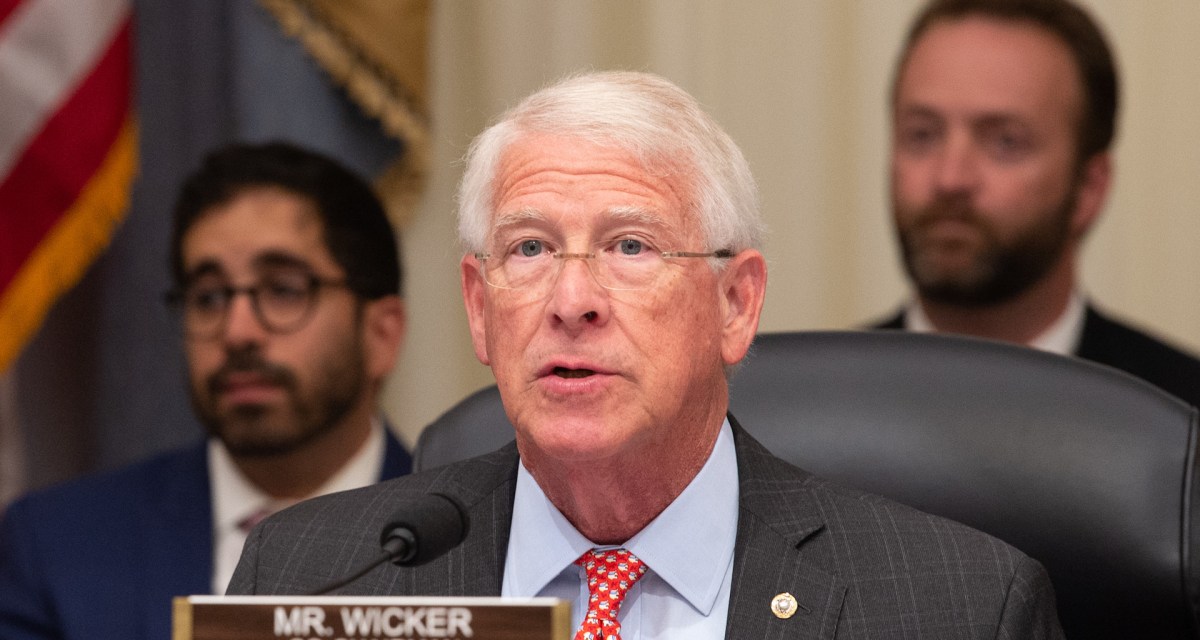
A report released Thursday by the Senate Commerce Committee expands on information about the breach, which was first reported in a recent audit by the CPSC’s inspector general. The incident stemmed from “a lack of formal training, ineffective management, and poor information technology implementation at CPSC rather than deliberate malfeasance by CPSC employees,” committee Chairman Roger Wicker, R-Miss., wrote in a letter to CPSC’s leadership.
Sometime between December of 2017 and March 22, 2019, the report states, the CPSC clearinghouse released data on reported injuries or deaths associated with consumer products to various outside entities, including the publication Consumer Reports and “a Researcher at Texas A&M University.” The problem? PII on manufacturers and consumers had not been redacted from the data before release, as required by the Consumer Product Safety Act of 1972. The PII included street addresses, ages and genders.
The Commerce Committee found out about the disclosures in April, and began investigating.
The committee’s majority staff found that the issue is “likely attributable to incompetence and mismanagement rather than deliberate, bad-faith efforts by senior managers or commissioners.” At least part of this has to do with the three different software systems that employees must use to access data. Per the report, in addition to one of these systems being a legacy system that was supposed to be retired “years ago,” “it is not always clear to frontline employees which application to use for a given project.”
Employees also were not trained regularly and consistently on the expectations to redact PII before release of data, the report says.
Ultimately, the committee recommends that CPSC implement a formal training process, and simplify its IT systems for data access.
The “root causes” of the breach “have not been fully identified,” the report says, but “it is extremely likely that CPSC will need to consider a wide variety of process changes in addition to implementing new IT-based solutions to mitigate the risk of future incidents.”






